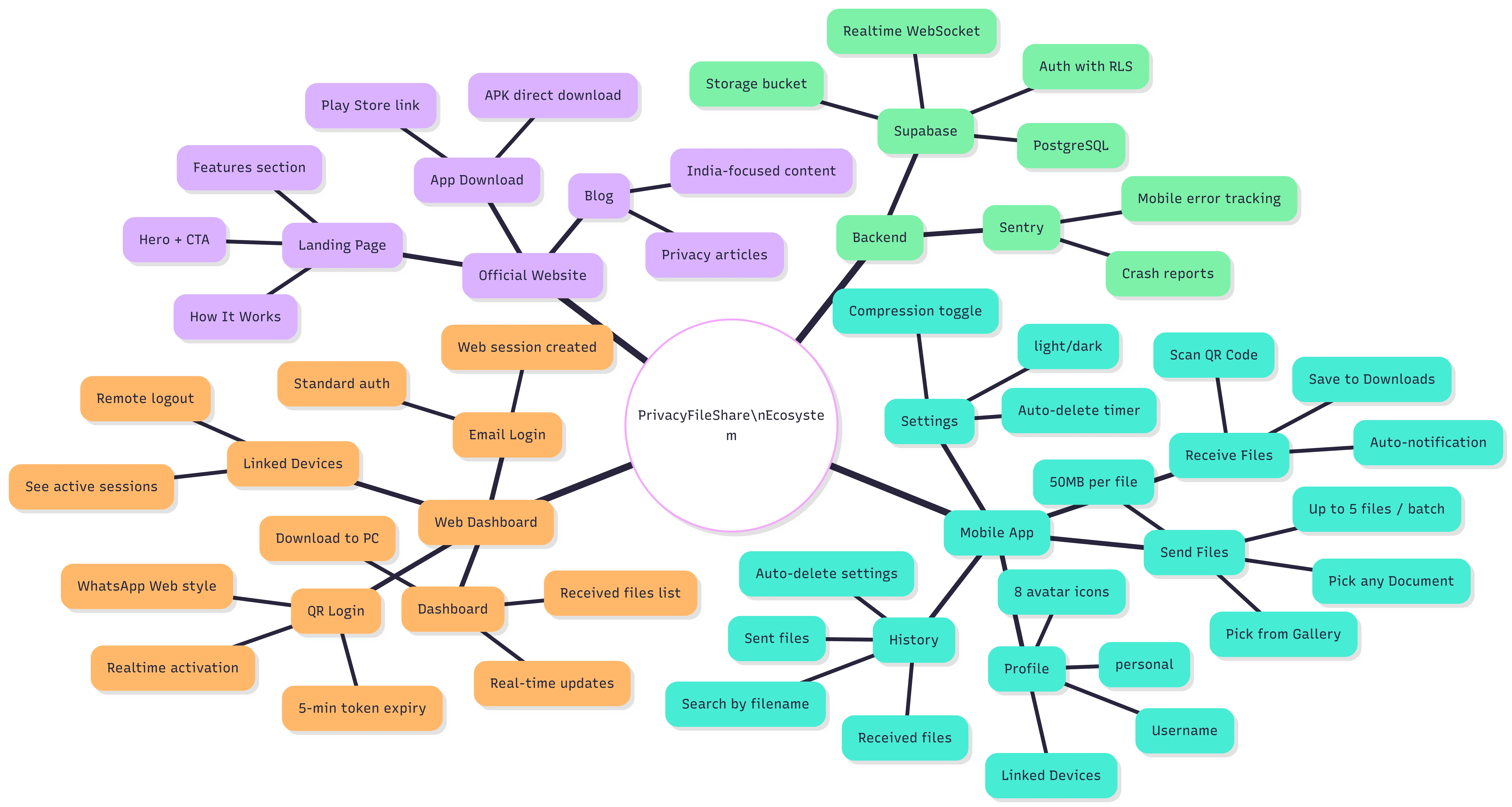
PrivacyFileShare is an Android-first SaaS platform designed to eliminate the friction and privacy risk of conventional file sharing. Most file-sharing tools require both parties to expose their contact details phone numbers or email addresses creating an unnecessary digital footprint.
This project tackles that problem head-on: users generate a short-lived, anonymous link tied to no personal identity. The recipient downloads the file using only the link, and the file is purged after transfer. No accounts. No traces.
The primary challenge was designing a zero-identity file transfer system one where both sender and receiver remain completely anonymous while still ensuring the transfer is secure, fast, and tamper-proof.
Key technical hurdles included:
The solution centers around a tokenized, ephemeral transfer model. When a user selects a file, the backend generates a cryptographically random token and stores the file temporarily in an isolated Supabase Storage bucket with no metadata linking back to the uploader.
The receiver enters or scans the token in the Android app or on the web interface, retrieves the file, and the record is automatically deleted post-download (or after expiry). Key decisions:
Firebase's real-time listeners made token-state tracking trivial listening for a "consumed" flag change triggers instant cleanup without polling.
Privacy is enforced through anonymity and access control rather than client-side encryption. Files are transmitted over TLS (HTTPS), stored with Supabase server-side encryption, and protected by strict Row-Level Security — no identity is ever attached to a transfer.
Serverless Edge Functions scale to zero and burst instantly a perfect fit for a product with unpredictable, bursty traffic patterns.
Privacy is not a feature it is the product. Every architectural decision was evaluated through a privacy-first lens.
Mapped privacy requirements, defined threat model, and designed the zero-knowledge token scheme.
Built token generation, storage routing, and expiry enforcement as stateless serverless functions.
Developed the send/receive flows in React Native with secure HTTPS file transfer to Supabase Storage.
Stress-tested token collision rates, applied Firebase rules, and deployed to Vercel production.
The current architecture handles the MVP use case well. Planned evolutions: